- 8777701917
- info@saikatinfotech.com
- Basirhat W.B
SSL VPN full tunnel for remote user Fortinet
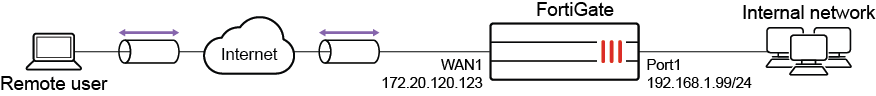
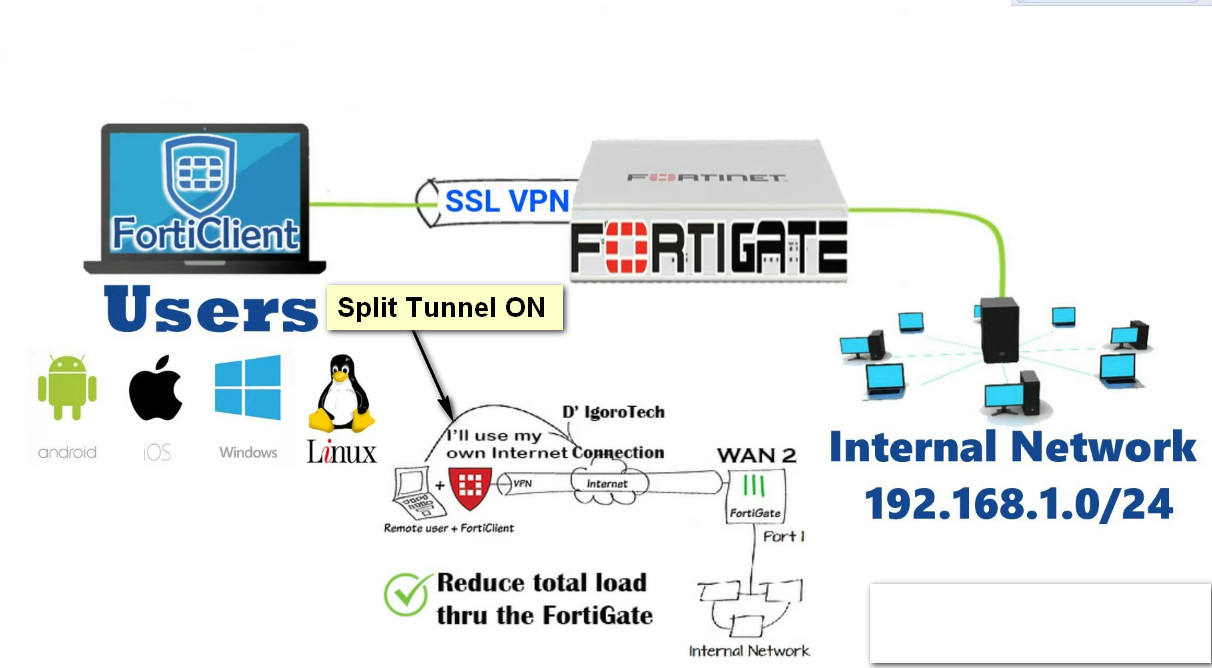
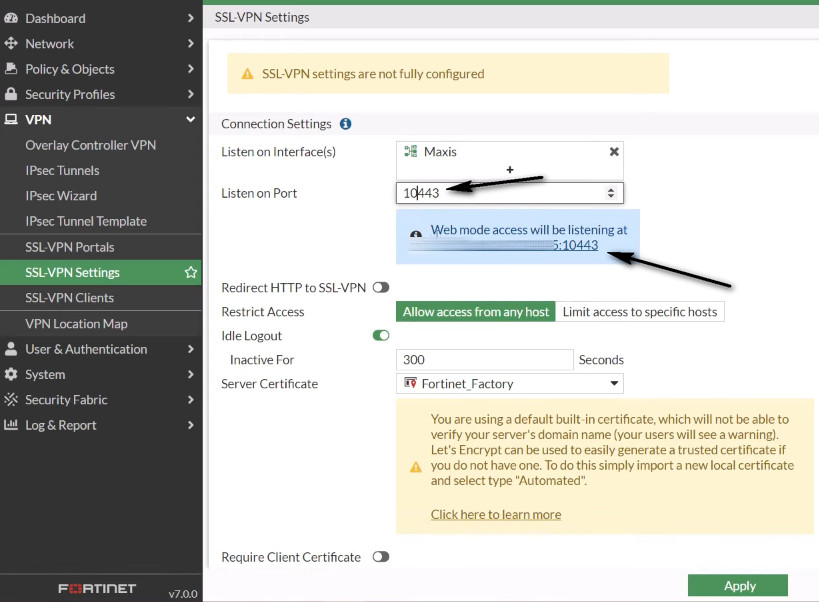
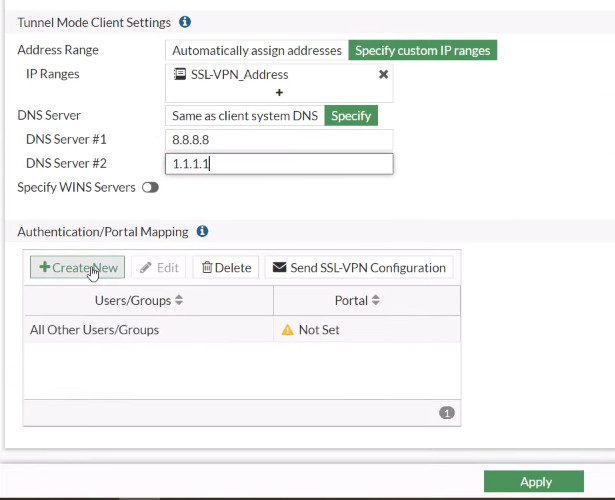
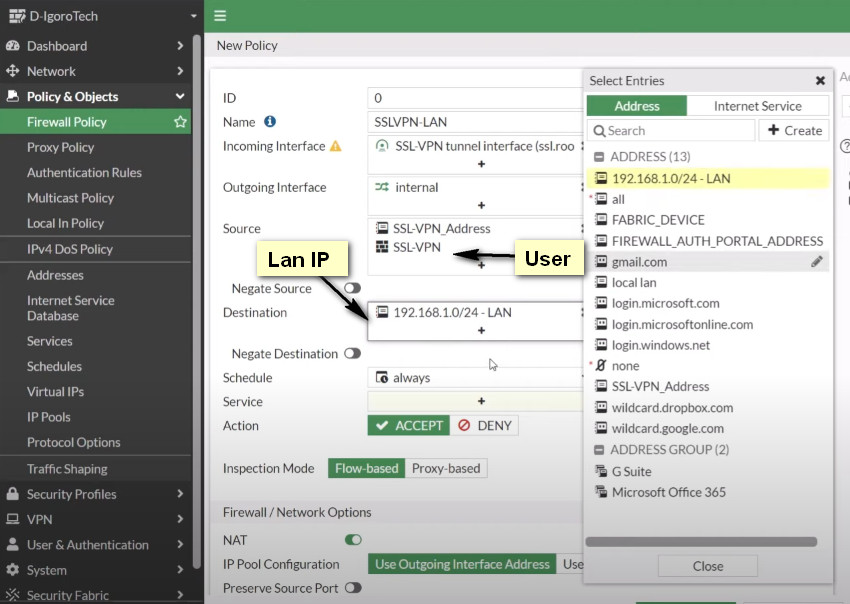
WAN interface is the interface connected to ISP. This example shows static mode. You can also use DHCP or PPPoE mode. The SSL VPN connection is established over the WAN interface. Ensure that SSL VPN feature visibility is enabled before starting the configuration.

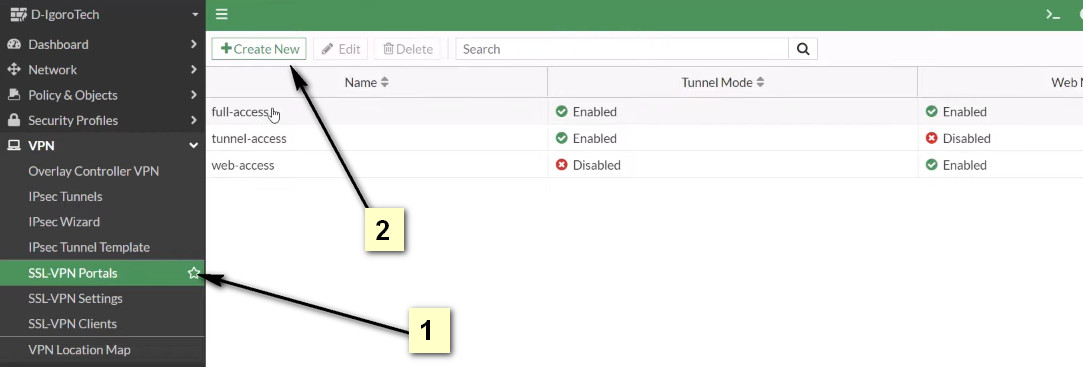
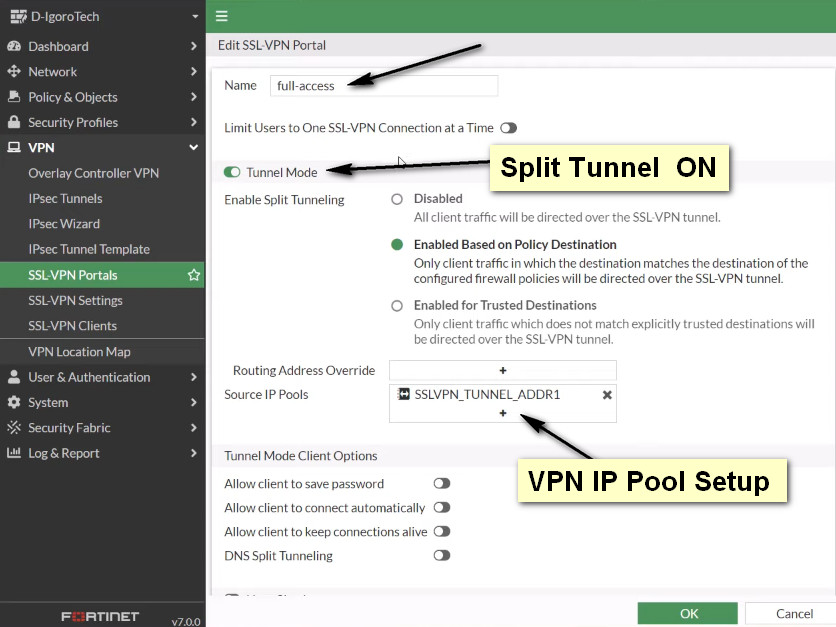
Click To full-access